Why is this important?
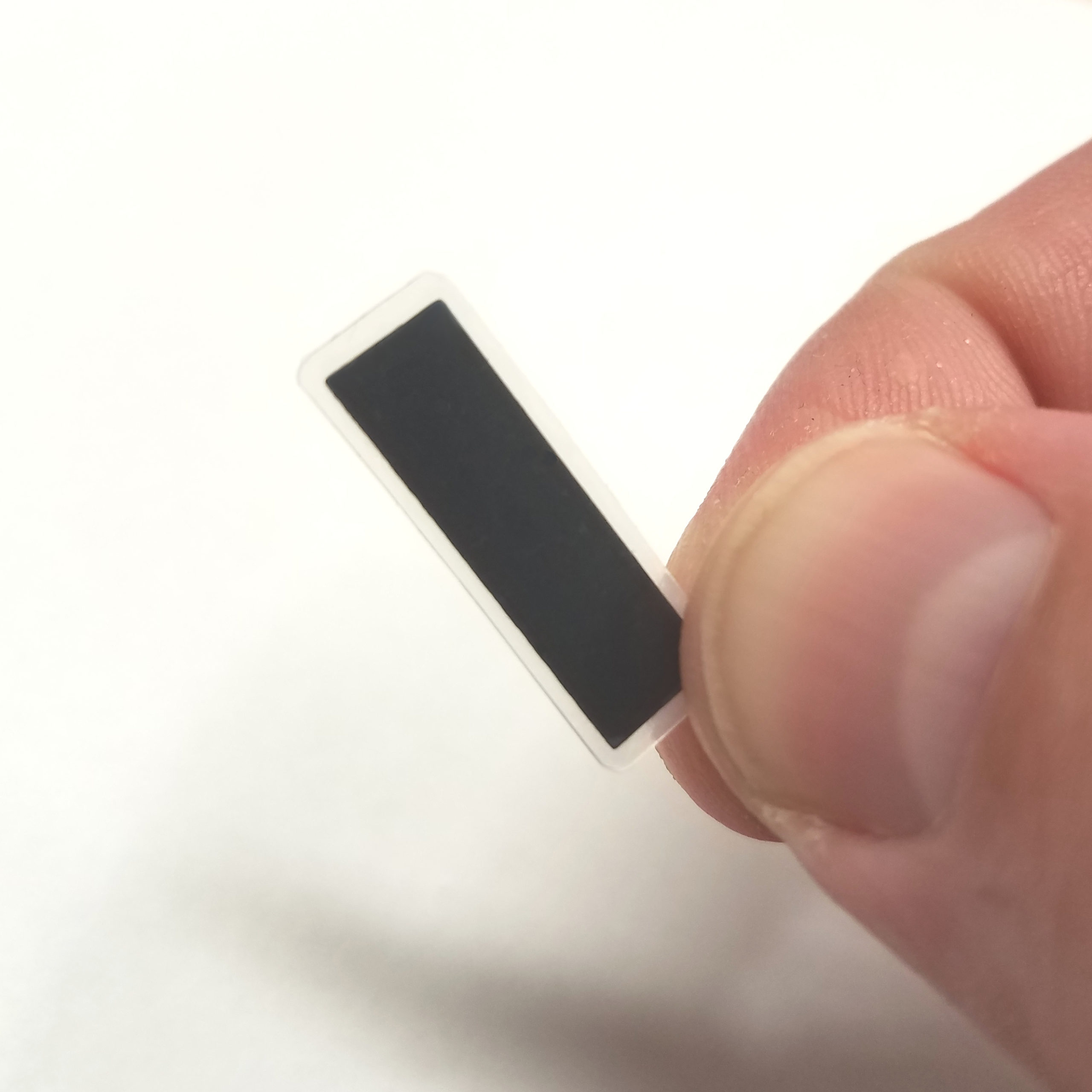
The NFC chip inside this product is an NTAG family chip from NXP. This chip type was designed for use in more typical NFC applications such as smart posters, labels, and other disposable use cases where the memory contents would typically be written and then locked so it could not be changed. This is done using built-in “lock bytes” which are OTP (one time programmable). That means that once the lock bytes are turned on to protect memory blocks, they can never be unlocked. Once any memory block is locked, it will forever be read-only, which is not ideal for a chip implant. Also, many common NFC smartphone apps and software applications offer ways to “lock” or “protect” your tag, making it very easy to accidentally lock your implant as read-only.
Because of this, we have disabled the ability to change or set the lock bits in the NTAG chip inside this product.
In addition to lock bytes, the NTAG offers a 32bit password protection function. It can be used to password-protect just writing to or both reading from and writing to the user memory space of the NTAG chip. Regardless of what some NFC smartphone apps indicate, it is not possible to remove or disable the password, it is only possible to set the password to the factory default hexadecimal value of 0xFF 0xFF 0xFF 0xFF. If the password is not changed, and is set to the factory default, then anyone could easily authenticate, change your password, then write data or change protection options for your chip implant to lock you out of your own chip.
Because of this, we set a default password value of 0x44 0x4E 0x47 0x52 which is ASCII code for DNGR (some older batches of NExT chips have the password 0x4E 0x45 0x78 0x54 which is the ASCII code for NExT).
Finally, many of the critical configuration bytes used by NTAG chips are stored in the last few pages of the chip’s memory. This means that it may be possible for an NFC application that does not properly detect or honor the memory schema of the chip to accidentally attempt to write NDEF record data (the data you’re trying to store on the chip) overtop of the configuration bytes. For example, if the data you are attempting to write is longer than the memory pages available, the remainder of the data might be written overtop of configuration bytes, which contain settings that are potentially dangerous to modify. Accidentally writing to those memory pages could result in your chip’s configuration being irreversibly locked.
Because of this, we password-protect the configuration bytes from being able to be written to or updated by using the password feature of the NTAG chip. Your chip implant leaves our factory with the entire user memory space still fully accessible and writable, while at the same time the protect the configuration bytes and password values from being accidentally or maliciously overwritten.
Once your chip implant is installed, you’ll be able to use any NFC smartphone app to write data to the tag and not need to be afraid of accidentally locking the tag, or changing the configuration bytes, or someone maliciously locking your tag or changing your password. We suggest using NXP’s
TagWriter app.